peterthepigeon
Members-
Posts
112 -
Joined
-
Last visited
Everything posted by peterthepigeon
-
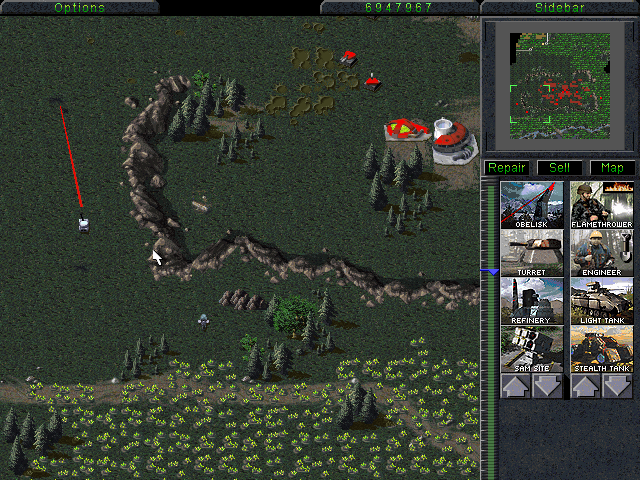
So now that my account is back and recovered. I'm starting a project to allow you to edit unit values as you would in RA, TS, etc. I may make a repo for the project, I haven't decided yet. Right now I'm just in the planning phase of the project, doing some UML, etc. The actual project will be coded in C++, and make use of regex, along with std::map and std::vector. For a project of this complexity, a parser is not required. Boost may be used, although maybe not as the STL provides everything I need. I plan to have a worker thread running every so often to query changes to the file and spit out any inconsistencies. In other words, you'll be able to alt tab out of the game to edit values on the fly and if it causes potential inconsistencies, they'll be discarded and the file overwritten with the last stable changes. It would be tempting to hardcode offsets and the like into the .dll itself, however, for ease of modification, simplicity sake and ease of development, I think I will simply keep it to .ini files. I plan to add a detours.ini, or something where you specify an offset, a detour type, or a modification in assembly and whether you allocate to a new RWX section or overwrite the opcodes in the .text section. I could use the heap for this, and then call VirtualProtect to mark the page RWX, however, I am not in 'love' with the idea, nor just willy nilly throwing out 4096 byte allocations. A memory manager seems most appropriate. This thread will be updated as I work on the project.
-
CPU Disasm Address Hex dump Command Comments 0041D1EC |. 8D4D AC LEA ECX,[EBP-54] 0041D1EF |. 8D5D A8 LEA EBX,[EBP-58] 0041D1F2 |. 8B55 B8 MOV EDX,DWORD PTR SS:[EBP-48] 0041D1F5 |. B8 C0DD5300 MOV EAX,0053DDC0 0041D1FA |. E8 A9520100 CALL 004324A8 ; [C&C95.004324A8 0041D1FF |. 8D4D B4 LEA ECX,[EBP-4C] 0041D202 |. 8D5D B0 LEA EBX,[EBP-50] 0041D205 |. 8B55 BC MOV EDX,DWORD PTR SS:[EBP-44] 0041D208 |. B8 C0DD5300 MOV EAX,0053DDC0 0041D20D |. E8 96520100 CALL 004324A8 ; [C&C95.004324A8 The lea just means pass by reference, from what I can see it takes a pointer to the map in EAX. void Compute ( void* mapptr, int unknown, short* a, short* b ) { // stuff goes here } This is what tells it where to draw the laser from and it's obviously related to cell computation or other drawing because I see this call referenced elsewhere. I haven't checked, nor do I really desire to spend too much time on it. The only question is what other input is necessary, and I'll examine that. Once you have this working it's a trivial matter to call drawline in the unit/infantry firing code to render the laser. This is the first real reverse engineering I've done in months on C&C. I'm lazy, get over it.
-
My favorite youtube channel made a video on TD.
peterthepigeon replied to CRITAWAKETS's topic in C&C 1
That's not a bad idea, commandos modified to auto capture certain structures and c4 the rest. -
The fact that you could fence the computer in and it does nothing.
-
A lot of WinAPi and hungarian notation, eh? Typical CnC hacker... Grow up. I hacked FPS games long before I took a whack at CnC. It's easy to determine whether a patch gives an advantage or not, just have a whitelist. Ergo, what are you talking about.
-
My disasm engine spits out mnemonics and the works. I'm tempted to do likewise for his executable. I'd copy the original code to the new section and set a check(config parsed at startup or new map) to execute original or jump over to the patched or nopped code, then back to the regular execution. Clean, simple and efficient. As for nasm files, meh, I'd just write my own mini assembler
-
I was wondering about that, the way you specified "unit code" and "Obelisk code" separately... though that's the same code for the same address, just called with different vtables. Meh. I'd have to look into the exe to properly parse this. To be honest it's probably better just to patch the unit code to call drawline. That's the route I intend to go.
-
or in other words, 0, 2 Rearranging stupidly cause well it's fun, only works on 0 and 2 also. 2x = x^2 x = ( ( x^2 ) / 2) Alternatively you could just realize this is a quadratic form also. ax^2 + bx + C = 0 ( x^2 - 2x ) = 0 factor out the x x ( x - 2 ) = 0
-
I honestly would recommend duplicating the code paths and redirecting to a new section, make sure of course to properly handle relocations. I could do this myself and maybe I will when I feel like it.
-
The hackishness of your patched executable versus the clean pristine one to notate all your patches.
-
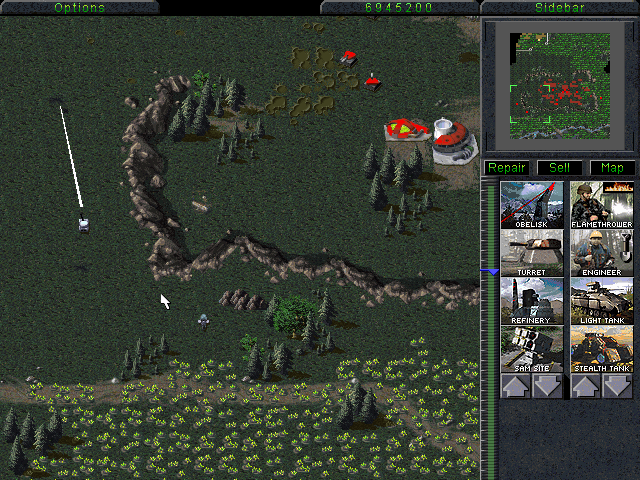
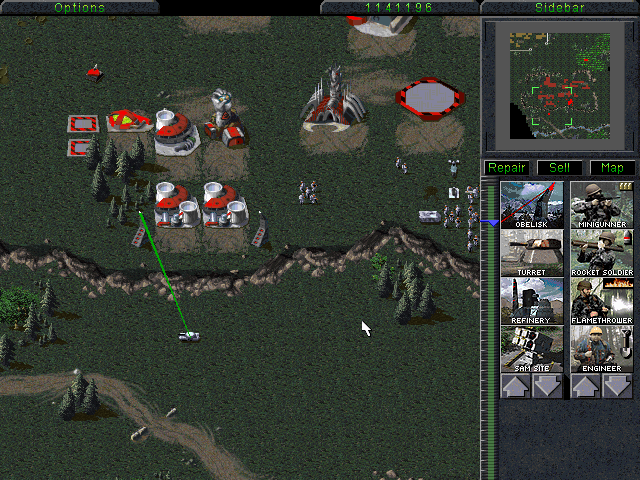
Keep in mind this is extremely hacky and I haven't worked beyond this, but it does work and on the move the laser sometimes may not draw at all.
-
Start by finding the call that handles the firing code. 00471197 FF92 04010000 CALL DWORD PTR DS:[EDX+104] Notice that it's a vtable. The code for structures is at: 004211CC 53 PUSH EBX However notice that if we immediately patch it, guess what? We crash at: 004211DB 8A40 54 MOV AL,BYTE PTR DS:[EAX+54] So even if we nop it out, or patch it to find the unit location in memory we still don't see the laser drawn. The answer is straight forward. 00421213 2E:FF2485 A0114200 JMP DWORD PTR CS:[EAX*4+4211A0] ; C&C95.00421265 We must zero out eax, so a simple unit or infantry check and done. No laser? Oh my. We breakpoint on where we're supposed to: Unit code 0042177E FF91 BC010000 CALL DWORD PTR DS:[ECX+1BC] ; C&C95.004B6120 Obelisk code 0042177E FF91 BC010000 CALL DWORD PTR DS:[ECX+1BC] ; C&C95.0041D058 More entry replacement. Then we crash again. 0041D06F 8B58 42 MOV EBX,DWORD PTR DS:[EAX+42] Nop or fix accordingly. 0041D0C0 8A40 54 MOV AL,BYTE PTR DS:[EAX+54] Ditto. You'll have to adjust some of the jump paths, but it should start drawing. Presto done.
-
CreateFile on both files ReadFile on both get offset to code section iterate until through ( *pbOldCodeSection != *pbPatchedCodesection ) notate accordingly simple
-
Changing macros, expanding memory foot print, that's a lot of work. Then making sure units and structures that are in the expanded regions remain inactive. Lots of work.
-
42 is best cause it's the answer to everything
-
FFA that turns to double teaming is called Murphy's Law. Now to counter I employ my own Murphy's Law. Want to 5v1 me in a FFA? 4 will immediately surrender, no questions asked. I don't play fair if you don't play fair, it's that simple.
-
I'll post how I did it, when I have some time after what I'm working on is finished.
-
Favorite: AtomicDn Least Favorite: AtomicUp
-
Vtables and jumptables yes.
-
Entry replacement, couple of byte patches and presto, it works. Easy peasy. Quite.
-
-
-
CPU Disasm Address Hex dump Command Comments 0041D1B5 |. 8D46 2F LEA EAX,[ESI+2F] 0041D1B8 |. 31D2 XOR EDX,EDX 0041D1BA |. C640 02 00 MOV BYTE PTR DS:[EAX+2],0 0041D1BE |. 66:8910 MOV WORD PTR DS:[EAX],DX 0041D1C1 |. 8A50 02 MOV DL,BYTE PTR DS:[EAX+2] 0041D1C4 |. 8D5D BC LEA EBX,[LOCAL.20] 0041D1C7 |. 8850 03 MOV BYTE PTR DS:[EAX+3],DL 0041D1CA |. 8D55 B8 LEA EDX,[LOCAL.21] 0041D1CD |. B8 C0DD5300 MOV EAX,0053DDC0 0041D1D2 |. E8 5D540100 CALL 00432634 ; [C&C95.00432634 0041D1D7 |. 85C0 TEST EAX,EAX 0041D1D9 |. 0F84 45020000 JE 0041D424 0041D1DF |. 803D 041E5400 00 CMP BYTE PTR DS:[541E04],0 0041D1E6 |. 0F85 38020000 JNE 0041D424 0041D1EC |. 8D4D AC LEA ECX,[LOCAL.24] 0041D1EF |. 8D5D A8 LEA EBX,[LOCAL.25] 0041D1F2 |. 8B55 B8 MOV EDX,DWORD PTR SS:[LOCAL.21] 0041D1F5 |. B8 C0DD5300 MOV EAX,0053DDC0 0041D1FA |. E8 A9520100 CALL 004324A8 ; [C&C95.004324A8 0041D1FF |. 8D4D B4 LEA ECX,[LOCAL.22] 0041D202 |. 8D5D B0 LEA EBX,[LOCAL.23] 0041D205 |. 8B55 BC MOV EDX,DWORD PTR SS:[LOCAL.20] 0041D208 |. B8 C0DD5300 MOV EAX,0053DDC0 0041D20D |. E8 96520100 CALL 004324A8 ; [C&C95.004324A8 0041D212 |. 8B5D A8 MOV EBX,DWORD PTR SS:[LOCAL.25] 0041D215 |. 8B4D B0 MOV ECX,DWORD PTR SS:[LOCAL.23] 0041D218 |. 8B7D AC MOV EDI,DWORD PTR SS:[LOCAL.24] 0041D21B |. A1 ECDE5300 MOV EAX,DWORD PTR DS:[53DEEC] 0041D220 |. 8B55 B4 MOV EDX,DWORD PTR SS:[LOCAL.22] 0041D223 |. 01C3 ADD EBX,EAX 0041D225 |. 01C1 ADD ECX,EAX 0041D227 |. A1 F0DE5300 MOV EAX,DWORD PTR DS:[53DEF0] 0041D22C |. 895D A8 MOV DWORD PTR SS:[LOCAL.25],EBX 0041D22F |. 894D B0 MOV DWORD PTR SS:[LOCAL.23],ECX 0041D232 |. 01C7 ADD EDI,EAX 0041D234 |. 01C2 ADD EDX,EAX 0041D236 |. B8 001C5400 MOV EAX,00541C00 0041D23B |. 897D AC MOV DWORD PTR SS:[LOCAL.24],EDI 0041D23E |. 8955 B4 MOV DWORD PTR SS:[LOCAL.22],EDX 0041D241 |. E8 EAC80A00 CALL 004C9B30 ; [C&C95.004C9B30 0041D246 |. 8B45 A8 MOV EAX,DWORD PTR SS:[LOCAL.25] 0041D249 |. 40 INC EAX 0041D24A |. 8945 D0 MOV DWORD PTR SS:[LOCAL.15],EAX 0041D24D |. 8B45 AC MOV EAX,DWORD PTR SS:[LOCAL.24] 0041D250 |. 8945 D4 MOV DWORD PTR SS:[LOCAL.14],EAX 0041D253 |. 8B45 B0 MOV EAX,DWORD PTR SS:[LOCAL.23] 0041D256 |. 8B3D 2C275A00 MOV EDI,DWORD PTR DS:[5A272C] 0041D25C |. 8945 98 MOV DWORD PTR SS:[LOCAL.29],EAX 0041D25F |. 8B45 B4 MOV EAX,DWORD PTR SS:[LOCAL.22] 0041D262 B6 7D MOV DH,7D 0041D264 |. 8945 94 MOV DWORD PTR SS:[LOCAL.30],EAX 0041D267 |. 8B47 1C MOV EAX,DWORD PTR DS:[EDI+1C] 0041D26A |. 8875 FC MOV BYTE PTR SS:[LOCAL.4],DH 0041D26D |. E8 CEC80A00 CALL 004C9B40 ; [C&C95.004C9B40 0041D272 |. 85C0 TEST EAX,EAX 0041D274 |. 74 22 JE SHORT 0041D298 0041D276 |. 3B7F 1C CMP EDI,DWORD PTR DS:[EDI+1C] 0041D279 |. 74 18 JE SHORT 0041D293 0041D27B |. 8B4F 08 MOV ECX,DWORD PTR DS:[EDI+8] 0041D27E |. 8B47 04 MOV EAX,DWORD PTR DS:[EDI+4] 0041D281 |. 51 PUSH ECX ; /Arg2 0041D282 |. 8B5F 10 MOV EBX,DWORD PTR DS:[EDI+10] ; | 0041D285 |. 8B57 1C MOV EDX,DWORD PTR DS:[EDI+1C] ; | 0041D288 |. 50 PUSH EAX ; |Arg1 0041D289 |. 8B4F 14 MOV ECX,DWORD PTR DS:[EDI+14] ; | 0041D28C |. 89F8 MOV EAX,EDI ; | 0041D28E |. E8 35C50A00 CALL 004C97C8 ; \C&C95.004C97C8 0041D293 |> B8 01000000 MOV EAX,1 0041D298 |> 85C0 TEST EAX,EAX 0041D29A |. 74 1F JE SHORT 0041D2BB 0041D29C |. 31C0 XOR EAX,EAX 0041D29E |. 8A45 FC MOV AL,BYTE PTR SS:[LOCAL.4] 0041D2A1 |. 50 PUSH EAX 0041D2A2 |. 8B55 94 MOV EDX,DWORD PTR SS:[LOCAL.30] 0041D2A5 |. 52 PUSH EDX 0041D2A6 |. 8B5D 98 MOV EBX,DWORD PTR SS:[LOCAL.29] 0041D2A9 |. 53 PUSH EBX 0041D2AA |. 8B4D D4 MOV ECX,DWORD PTR SS:[LOCAL.14] 0041D2AD |. 51 PUSH ECX 0041D2AE |. 8B45 D0 MOV EAX,DWORD PTR SS:[LOCAL.15] 0041D2B1 |. 50 PUSH EAX 0041D2B2 |. 57 PUSH EDI 0041D2B3 E8 28100B00 CALL 004CE2E0 0041D2B8 |. 83C4 18 ADD ESP,18 0041D2BB |> 8B47 1C MOV EAX,DWORD PTR DS:[EDI+1C] 0041D2BE |. E8 8DC90A00 CALL 004C9C50 ; [C&C95.004C9C50 0041D2C3 |. 85C0 TEST EAX,EAX 0041D2C5 |. 74 16 JE SHORT 0041D2DD 0041D2C7 |. 8B57 1C MOV EDX,DWORD PTR DS:[EDI+1C] 0041D2CA |. 39D7 CMP EDI,EDX 0041D2CC |. 74 0F JE SHORT 0041D2DD 0041D2CE |. 837F 20 00 CMP DWORD PTR DS:[EDI+20],0 0041D2D2 |. 74 09 JE SHORT 0041D2DD 0041D2D4 |. 8B4A 24 MOV ECX,DWORD PTR DS:[EDX+24] 0041D2D7 |. 85C9 TEST ECX,ECX 0041D2D9 |. 75 02 JNE SHORT 0041D2DD 0041D2DB |. 890F MOV DWORD PTR DS:[EDI],ECX 0041D2DD |> 8B45 A8 MOV EAX,DWORD PTR SS:[LOCAL.25] 0041D2E0 |. 48 DEC EAX 0041D2E1 |. 8945 E0 MOV DWORD PTR SS:[LOCAL.11],EAX 0041D2E4 |. 8B45 AC MOV EAX,DWORD PTR SS:[LOCAL.24] 0041D2E7 |. 8945 A4 MOV DWORD PTR SS:[LOCAL.26],EAX 0041D2EA |. 8B45 B0 MOV EAX,DWORD PTR SS:[LOCAL.23] 0041D2ED |. 8B3D 2C275A00 MOV EDI,DWORD PTR DS:[5A272C] 0041D2F3 |. 8945 C8 MOV DWORD PTR SS:[LOCAL.17],EAX 0041D2F6 |. 8B45 B4 MOV EAX,DWORD PTR SS:[LOCAL.22] 0041D2F9 B3 7D MOV BL,7D 0041D2FB |. 8945 C4 MOV DWORD PTR SS:[LOCAL.18],EAX 0041D2FE |. 8B47 1C MOV EAX,DWORD PTR DS:[EDI+1C] 0041D301 |. 885D F4 MOV BYTE PTR SS:[LOCAL.6],BL 0041D304 |. E8 37C80A00 CALL 004C9B40 ; [C&C95.004C9B40 0041D309 |. 85C0 TEST EAX,EAX 0041D30B |. 74 23 JE SHORT 0041D330 0041D30D |. 8B47 1C MOV EAX,DWORD PTR DS:[EDI+1C] 0041D310 |. 39C7 CMP EDI,EAX 0041D312 |. 74 17 JE SHORT 0041D32B 0041D314 |. 8B57 08 MOV EDX,DWORD PTR DS:[EDI+8] 0041D317 |. 52 PUSH EDX ; /Arg2 0041D318 |. 8B5F 04 MOV EBX,DWORD PTR DS:[EDI+4] ; | 0041D31B |. 8B4F 14 MOV ECX,DWORD PTR DS:[EDI+14] ; | 0041D31E |. 53 PUSH EBX ; |Arg1 0041D31F |. 89C2 MOV EDX,EAX ; | 0041D321 |. 89F8 MOV EAX,EDI ; | 0041D323 |. 8B5F 10 MOV EBX,DWORD PTR DS:[EDI+10] ; | 0041D326 |. E8 9DC40A00 CALL 004C97C8 ; \C&C95.004C97C8 0041D32B |> B8 01000000 MOV EAX,1 0041D330 |> 85C0 TEST EAX,EAX 0041D332 |. 74 1F JE SHORT 0041D353 0041D334 |. 31C0 XOR EAX,EAX 0041D336 |. 8A45 F4 MOV AL,BYTE PTR SS:[LOCAL.6] 0041D339 |. 50 PUSH EAX 0041D33A |. 8B4D C4 MOV ECX,DWORD PTR SS:[LOCAL.18] 0041D33D |. 51 PUSH ECX 0041D33E |. 8B45 C8 MOV EAX,DWORD PTR SS:[LOCAL.17] 0041D341 |. 50 PUSH EAX 0041D342 |. 8B55 A4 MOV EDX,DWORD PTR SS:[LOCAL.26] 0041D345 |. 52 PUSH EDX 0041D346 |. 8B5D E0 MOV EBX,DWORD PTR SS:[LOCAL.11] 0041D349 |. 53 PUSH EBX 0041D34A |. 57 PUSH EDI 0041D34B E8 900F0B00 CALL 004CE2E0 0041D350 83C4 18 ADD ESP,18 0041D353 8B47 1C MOV EAX,DWORD PTR DS:[EDI+1C] 0041D356 |. E8 F5C80A00 CALL 004C9C50 0041D35B |. 85C0 TEST EAX,EAX 0041D35D |. 74 16 JE SHORT 0041D375 0041D35F |. 8B4F 1C MOV ECX,DWORD PTR DS:[EDI+1C] 0041D362 |. 39CF CMP EDI,ECX 0041D364 |. 74 0F JE SHORT 0041D375 0041D366 |. 837F 20 00 CMP DWORD PTR DS:[EDI+20],0 0041D36A |. 74 09 JE SHORT 0041D375 0041D36C |. 8B51 24 MOV EDX,DWORD PTR DS:[ECX+24] 0041D36F |. 85D2 TEST EDX,EDX 0041D371 |. 75 02 JNE SHORT 0041D375 0041D373 8917 MOV DWORD PTR DS:[EDI],EDX 0041D375 8B45 A8 MOV EAX,DWORD PTR SS:[EBP-58] 0041D378 8945 DC MOV DWORD PTR SS:[EBP-24],EAX 0041D37B 8B45 AC MOV EAX,DWORD PTR SS:[EBP-54] 0041D37E 8945 A0 MOV DWORD PTR SS:[EBP-60],EAX 0041D381 8B45 B0 MOV EAX,DWORD PTR SS:[EBP-50] 0041D384 8B3D 2C275A00 MOV EDI,DWORD PTR DS:[5A272C] 0041D38A 8945 9C MOV DWORD PTR SS:[EBP-64],EAX 0041D38D 8B45 B4 MOV EAX,DWORD PTR SS:[EBP-4C] 0041D390 B7 03 MOV BH,3 0041D392 |. 8945 C0 MOV DWORD PTR SS:[LOCAL.19],EAX 0041D395 |. 8B47 1C MOV EAX,DWORD PTR DS:[EDI+1C] 0041D398 |. 887D F8 MOV BYTE PTR SS:[LOCAL.5],BH 0041D39B |. E8 A0C70A00 CALL 004C9B40 ; [C&C95.004C9B40 0041D3A0 |. 85C0 TEST EAX,EAX 0041D3A2 |. 74 22 JE SHORT 0041D3C6 0041D3A4 |. 3B7F 1C CMP EDI,DWORD PTR DS:[EDI+1C] 0041D3A7 |. 74 18 JE SHORT 0041D3C1 0041D3A9 |. 8B4F 08 MOV ECX,DWORD PTR DS:[EDI+8] 0041D3AC |. 8B47 04 MOV EAX,DWORD PTR DS:[EDI+4] 0041D3AF |. 51 PUSH ECX ; /Arg2 0041D3B0 |. 8B5F 10 MOV EBX,DWORD PTR DS:[EDI+10] ; | 0041D3B3 |. 8B57 1C MOV EDX,DWORD PTR DS:[EDI+1C] ; | 0041D3B6 |. 50 PUSH EAX ; |Arg1 0041D3B7 |. 8B4F 14 MOV ECX,DWORD PTR DS:[EDI+14] ; | 0041D3BA |. 89F8 MOV EAX,EDI ; | 0041D3BC |. E8 07C40A00 CALL 004C97C8 ; \C&C95.004C97C8 0041D3C1 |> B8 01000000 MOV EAX,1 0041D3C6 |> 85C0 TEST EAX,EAX 0041D3C8 |. 74 1F JE SHORT 0041D3E9 0041D3CA |. 31C0 XOR EAX,EAX 0041D3CC 8A45 F8 MOV AL,BYTE PTR SS:[EBP-8] 0041D3CF 50 PUSH EAX 0041D3D0 8B55 C0 MOV EDX,DWORD PTR SS:[EBP-40] 0041D3D3 |. 52 PUSH EDX 0041D3D4 8B5D 9C MOV EBX,DWORD PTR SS:[EBP-64] 0041D3D7 53 PUSH EBX 0041D3D8 8B4D A0 MOV ECX,DWORD PTR SS:[EBP-60] 0041D3DB |. 51 PUSH ECX 0041D3DC |. 8B45 DC MOV EAX,DWORD PTR SS:[LOCAL.12] 0041D3DF |. 50 PUSH EAX 0041D3E0 |. 57 PUSH EDI 0041D3E1 E8 FA0E0B00 CALL 004CE2E0 0041D3E6 |. 83C4 18 ADD ESP,18 I practically gave it away earlier :/ http://cnc-comm.com/community/index.php?topic=3150.msg26759#msg26759 Green lasers.
-
Weird Discovery (or I live under a rock in tiberium land)
peterthepigeon replied to MattAttack's topic in C&C 1
The AI has to be 'told' to build medium tanks.